How to Enable the Success of DevSecOps in Your Organization
by Josh Biggs in Tech on 3rd December 2020In today’s fast-paced SDLC environment, getting the finished product out the door is the priority for enterprises. Adding to this is the ever-evolving technological landscape. This balancing act on strict deadlines may leave space open for security oversights in the code being produced.
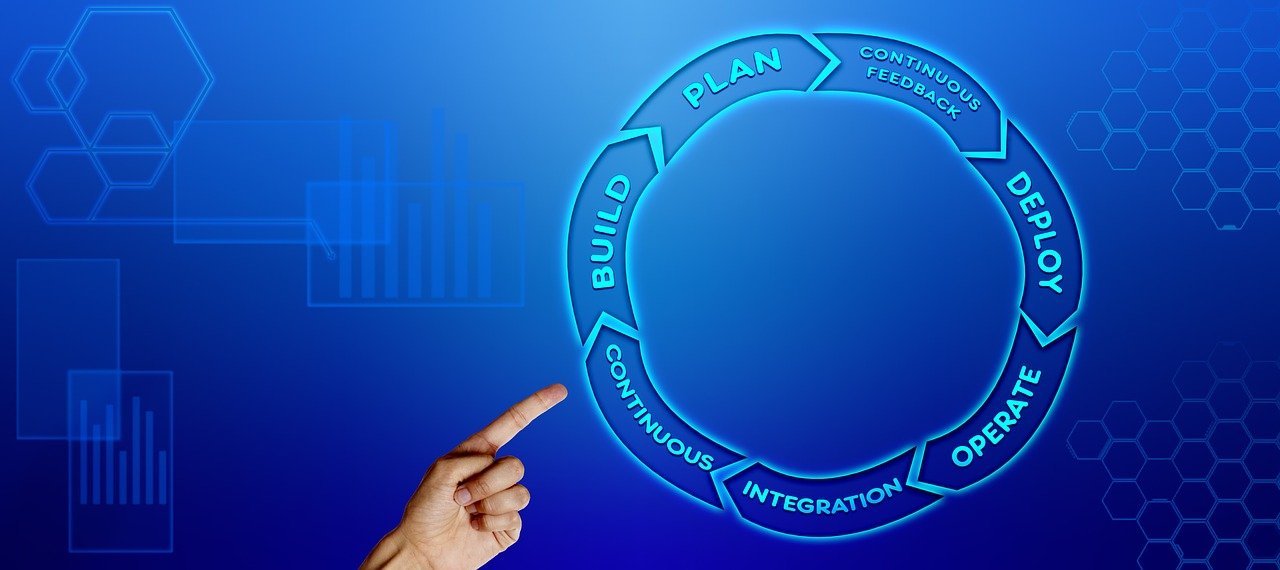
Quality assessment is insufficient in overcoming this problem if it doesn’t incorporate security measures. This new DevSecOps ensures that security features become the byproduct of the development process rather than an adjunct one. It will bridge the different stages and associated departments of DevOps under one security umbrella.
Steps to Get the Best DevSecOps Enabled
A successful security process implementation into the DevOps pipeline is a team effort that needs coordination between various stakeholders. And coordination is best achieved by the rigorous following of certain steps which can guide in that process. These vary with time and technological changes, ensuring they are always up-to-date, unlike traditional practices.
Selecting the Right Tools
Any task is best accomplished when the correct tools are used for it such as log management tools. The same is the case with development. The challenge while opting for the right tool is balancing the cost, effectiveness, time to implement, and the tool’s age.
Security DevOps need tools that can be used in a dynamic setting; they should work as the development is occurring. They must keep pace with that development without giving out false positives, which would render them redundant. They must seamlessly integrate with the other tools used by the teams in the entire pipeline and must not bottleneck the flow due to synchronization issues.
Have Threat Foresight
It is always good to know your enemy before you fight them. Preliminary risk assessment and threat modeling will help you take stock of what’s at stake and how it can be attacked. It will help you check the effectiveness of present security measures and learn of the chinks in their armor which need to be patched.
It also gives you an insight into the basic structure of the application and the vulnerabilities embedded in it. While some might consider this process a burden and a speed bump in the fast-paced DevOps life cycle, it is essential to develop the roadmap for security integration and implementation.
Automation of All Possible Things
Developers can’t waste their time on manual testing and implementing security measures during the development process in a continuous integration/constant deployment (CI/CD) environment. Automation is the only way to go to make security process integration successful.
Tests and control setups for security must be attached from the very start to the end, and automation is the only efficient way to do it. This leaves the developer free to code while the automated security tool does its job in the background. Errors will be flagged in real-time, helping to correct them quickly and before they can cause further harm.
Some care must be taken, though. Running checks on entire applications at the end of each day (Static Application Security Testing or SAST) will slow down the entire operation, despite automation. Only the latest version/additions must be looked into. Dynamic Application Security Testing (DAST) is crucial for real-time security checks during application execution.
Ancillary tools can be added to augment the primary security ones’ functioning for better analysis and protection.
Detection in Dependent Software
Open-source software solutions are a favorite of all companies and their developers as they are cheap, free, and readily available. They, however, bring with them known or unknown vulnerabilities and risks. Your security protocol must take into account those as well when using these software systems.
DevOps has been a roaring success in the SDLC process everywhere, and DevSecOps works to close the gaps that might affect the finished product of that successful method.

